Filter by
News
|
2 Min Read
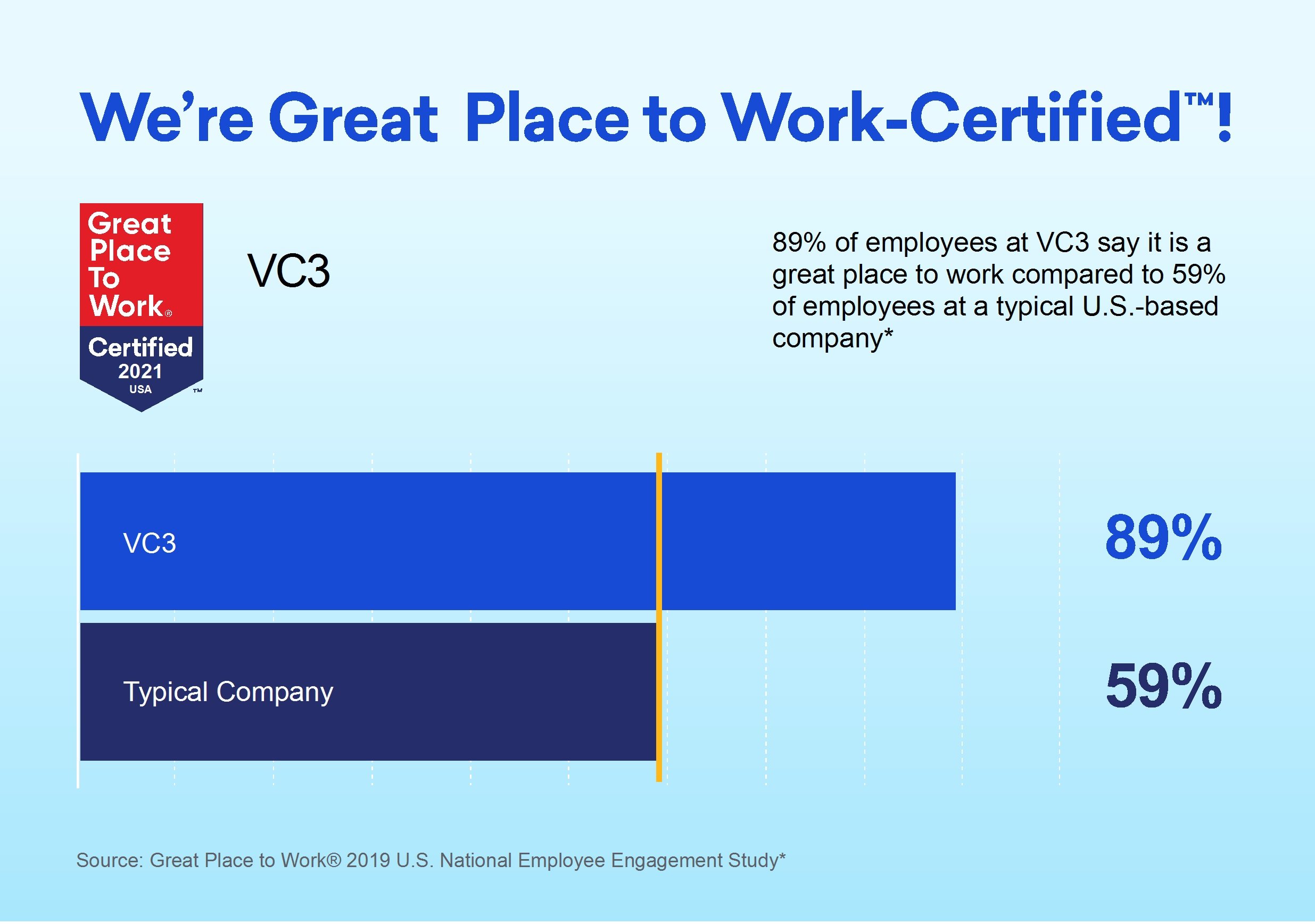
VC3 Earns 2024 Great Place To Work Certification™
VC3, a leading managed IT and cybersecurity services provider, is proud to be Certified™ by Great Place To Work® for the...
Read More

Team Member Spotlight
|
3 Min Read
[Inside VC3] Field Engineer/ Field Analyst: Out on the Frontline but Not Fl...
Field Engineers and Field Analysts at VC3 are IT professionals who swoop in and fix issues that can only be accomplished...
Read More

Blog
|
5 Min Read
Embracing the Future: AI’s Influence on Local Government
Municipalities are often data-rich in key areas. Envisioning some practical applications of AI within local government h...
Read More

Blog
|
3 Min Read
Still Relying on Antivirus? It’s No Longer Enough.
As cyber threats become increasingly sophisticated and frequent, it's essential for organizations to stay current with t...
Read More

Events
|
May 2, 2024
CMMC Educational Workshop: Teeing Up for CMMC Success: How to Evade the Top...
Join Corey Kaufman, Director of Client Strategy and Solutions at VC3, to learn about the top five challenges that compan...
Read More

Team Member Spotlight
|
2 Min Read
Inside VC3 – Onboarding Analyst Laying the Groundwork for Successful Suppor...
VC3 Onboarding Analysts who use their technical skills and communication expertise to get new client relationships start...
Read More
