Cyber security is much more than an IT problem these days - it's become a general business problem.
Before we dive in, let's remember that cyber security is not just a topic for large corporations. It affects EVERYONE, especially those in the small to mid-size business (SMB) market. The revelation of the Meltdown and Spectre vulnerabilities reminds us that cyber security affects everybody, individuals and businesses alike. Statistics are pointing towards hackers focusing a lot of energy on SMBs this year.
Why, you ask? Good question.
Historically speaking, SMBs haven't spent a lot of time trying to protect themselves. This leaves you ripe for easy attacks. Many times, the data collected by hackers has ties to larger corporations. Hackers use this as an entry point for an attack on the "bigger fish" you work with.
Let me explain.
Think back to when Target was hacked a few years ago. The HVAC contractor was exploited to gain access to Target's retail store network. The result: tens of thousands of credit card numbers leaked to the dark web. The hacker's “big fish” wasn’t Target themselves, but their shoppers’ credit card information was.
Businesses need to start taking a holistic look at the safety of their organization. This is an excellent opportunity to review things at your company.
What are the proper precautions? How can cybersecurity and information security be part of the culture of your business? Where should you start?
Let’s dive in.
Phase 1: What is a Business Approach to Cyber Security and Risk Management?
Shifting the way you approach cyber security to a general business problem is a game-changer. It will help you evaluate your company's safety from a holistic view.
Consider the balance between the availability of information and securing the information.
In today's world, it seems efficient to have shared information online. But have you considered the risks of exploitation? Portals and websites for your customers, vendors, or partners are convenient, but at what cost?
Have you thought about who's interested in your company or getting information from you? Or maybe it's not you at all; perhaps it's the customers in your database they want - like the Target example above.
Ultimately, the bad guy has an intricate attack scheme, and we need to be more vigilant. Your approach to business security practices has to evolve with them, or you risk significant loss.
Small Business Cyber Security Best Practices
The good thing about adopting this new approach is the things you were already doing still apply. The following are standard best practices that should already be in place at your company. If not, work with your IT department or managed service provider ASAP to get these measures up to date.
You must have endpoint detection and response on every device and every workstation. And it goes without saying that every server should have it as well. This includes Macs and all handheld devices, where applicable. Also, protect your network using firewalls and proper access policies. This includes tools that help keep undesired traffic out of your network.
Lastly (and most overlooked), you must update and patch old operating systems and your line of business software, such as your ERP or practice management software.
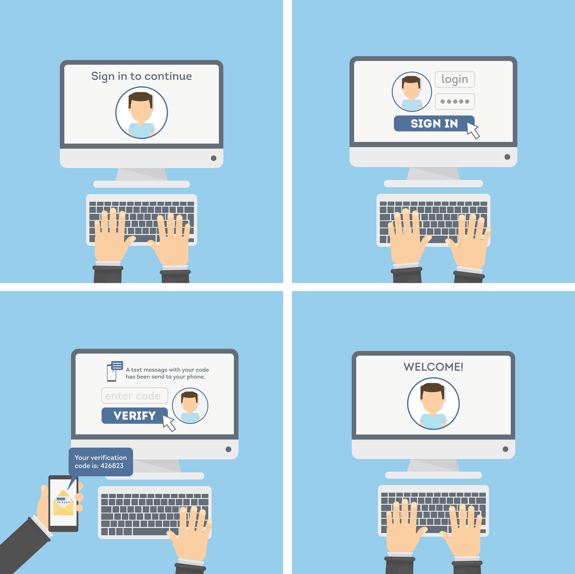
What's Next in Cyber Security Protection? Strong Passwords and Multi-Factor Authentication
You should have strong passwords, that's a given. But now we're moving into the era of multi-factor authentication. Moving forward you'll only be able to gain access to your sensitive data by first entering your password and then entering a code you receive via text. These codes generally have a 15-minute or less shelf-life and make it harder for hackers to get to your information.
Multi-Factor Authentication Example
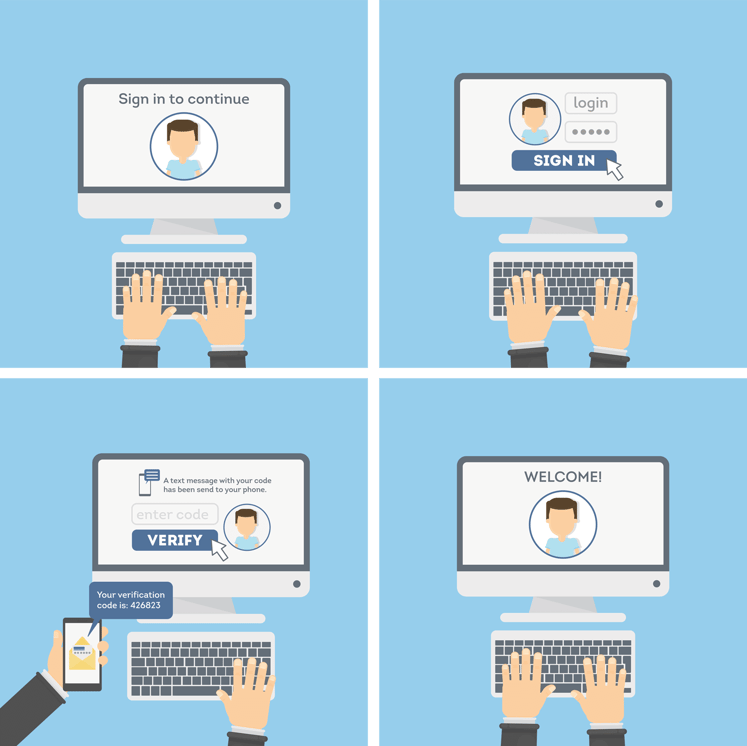
Creating a password protocol and following through with it on a company-wide level will be the first step in this equation. After that has been implemented, work with your IT department to add a multi-factor authentication process.
It may seem like a lot, but one small crack in your defenses and a hacker will find their way in.
Phase 2: Secure Your Business with Multi-Factor Internal Controls
The more significant discussion I'd like to get into is business practice and internal controls. Let's use accounting as our guinea pig.
Do your accounts payable systems have payment authorization over an absolute dollar limit? Or what about protocols for multi-person approval? Do you have an authorization process for online payments? Do you have a vetting process for online vendors? And let's not forget credit cards, do you allow them to be used on any website?
These are all areas where hackers can try to manipulate you via social engineering. Their goal is to either process a payment to steal your information or get you to pay money to the wrong person.
Unfortunately, this isn't just a cautionary tale. We see these scams play out far too often. And it's not careless people who are falling victim - without careful controls, it's happening to vigilant people too.
There are a lot of documented cases where improper business controls led businesses to shut their doors for good.
Train Employees How to Spot Cyber Attacks Before They Happen
To avoid significant issues, companies need to do a better job training their staff in cybersecurity. We'd suggest periodic training as part of your overall business strategy. Teach your employees what attacks and hackers look or sound like. It could be phishing emails or a phone call to accounting pretending to be a client. But don't stop there.
Once they know how to identify these scams, also teach them how to handle the incident if one ever does trick them into clicking.
This step is often overlooked. Many companies have all the right tools, firewalls, anti-spam, etc., but forget to train their employees.
Consider quarterly training. This would help keep best practices top of mind and help safeguard you from potential danger.
Physical Security Matters as Much as Network Security
Outside of what's lurking on the web, the general physical security of your company is a BIG deal. Most companies have a security system, so they don't always think about the physical facility beyond an alarm system.
Is your IT equipment locked away?
What about the accounting information?
And not just from outsiders, is it locked away from non-essential staff? Sometimes less is more, as in the fewer people with access, the less that could go wrong.
General employee access is often lost in translation. There should be policies about who gets access, as well as tracking measures. It's easy to get complacent when it comes to trust. And, while believing your employees are trustworthy, is great – but does your sales team really need access to payroll? Probably not.
There's also the threat of infiltrators -- and while you are not Fort Knox, let me explain.
Believe it or not, there have been several recorded cybersecurity breaches conducted by cleaning companies. You read the right, cleaning companies.
Criminals running fake cleaning companies wait for confidential documents to be left out or in a copy machine. They then steal your trade secrets and hold them for ransom, or worse, sell them to your competitors.
Things like clean desk policies are set up to keep employees from leaving confidential information out, for their safety and yours.
This brings us full circle. This is why cyber security should be classified as a general business problem. If cleaning companies can hack you, imagine who else could.
Phase 3: Cyber Security Management Planning
There is one more thing that small to mid-sized businesses can do to make their environment more secure: management. Having the right technical partner or managed service provider to handle everything is HUGE!
A lot of companies install or have these security measures in place, but don't know how to manage them properly. Unfortunately, they don't know the adequate response when there's a virus or an attack on their firewall.
Having the right partner to manage your environment moving forward takes an enormous burden off SMBs. IT isn't a "set it and forget it" kind of job; it's a living process that needs attention.
All these areas will be readily targeted vulnerabilities in the small to mid-sized business market. It's essential to safeguard your company from being exploited before it's too late. Make sure that you have all your bases covered when it comes to cybersecurity, not just bits and pieces.
And remember, cyber security isn't just an IT technology problem; you'll need a general business approach to protecting your whole company.
Have more questions? We're happy to chat anytime. Give us a call at 800-481-4369.