Email scams are almost as old as the internet itself, but the days of easily identifiable email scams are long gone. Today, cyber criminals are doing everything they can to trick unsuspecting recipients into clicking on a dangerous link or sharing sensitive information. Instead of a “Nigerian prince” asking for your bank info so they can transfer a million dollars to your account, scammers are posing as C-level executives and trusted vendors.
Now, it’s more important than ever to know what to look for in a scam email and how to keep yourself safe from cyber criminals.
In this article, we'll go through a few simple techniques that will help with your email security efforts:
- Creating a Secure Password
- How to Recognize and Avoid Phishing Email Scams
- Steps to Prevent Fraudulent Payments
So, let’s dive in.
Creating a Secure Password
Most people don’t think of passwords as powerful cyber security tools, but in reality, passwords are an easy and essential protection method.
Cyber criminals use tools that can guess thousands of passwords per minute. So, short common words or phrases make guessing passwords way too easy.
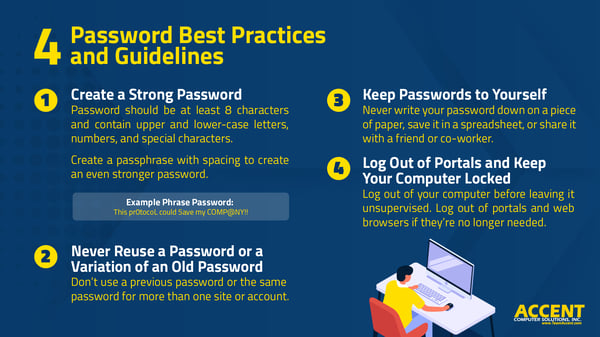
Here are some general rules to follow for creating a secure password:
- Start by using at least an 8-character password. Complexity isn’t necessarily better – length is the key today.
- If you can, try using a phrase with spaces and punctuation. Something like, “I love chocolate ice cream!”
- Use both upper and lower-case letters, special characters, and numbers when creating a password.
- Never use passwords that contain easily guessed words like “password” or “LetMeIn.”
- Avoid using creative ways to write the word ‘password,’ such as replacing the A with @ or the S with $.
- Avoid things like birthdays, commonly used phrases, and things that identify you or your company, such as your company name.
- Don’t reuse passwords. Create a different password for each app or website you log into.
How to Recognize and Avoid Phishing Email Scams
No matter how good your defenses are, phishing emails will still land in your inbox. Your best protection is knowing what to look for and what to do when you receive one. Learning how to recognize them is an essential skill that you will use daily.
As a general rule, we recommend visually scanning all emails for a few things before clicking attachments or links.
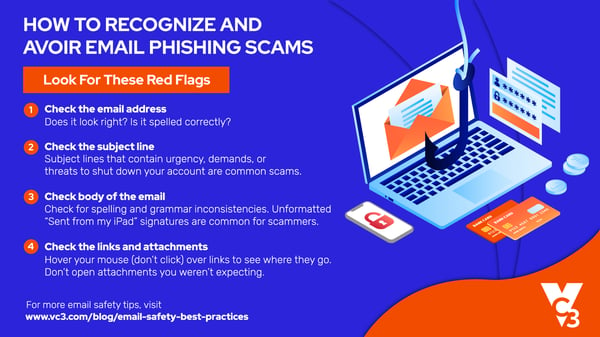
Here are some red flags to look for to spot fake emails:
Check the email address
Look for forged email addresses. In the Sent From line, hover your mouse over the email address. Does the address look real? Is everything spelled correctly? Is there anything skewed in the company name, like replacing an O with a zero?
Scammers have gotten very good at replicating actual companies, so double-check the sender before you do anything.
Also, be on the lookout for unexpected emails from people you know. Scammers are good at what they do. Pretending to be someone else is all a part of their game.
Check the subject line
Messages that contain threats to shut down your account, or ones that use words like “Urgent” to generate a false sense of importance, are usually scams. They’re using scare tactics to get you to act quickly and recklessly.
Check the body of the email
If you know what to look for, the body of an email has the most tell-tale signs. Look for poor writing or grammar -- scammers live all over the world and may not speak or read your language. They might rely on a free translation service that didn’t quite get it right. This is an excellent indicator that it’s a phishing attempt.
Requests for personal information are another sign. No legitimate service, company, or provider would ever ask for things like passwords, credit card numbers, or Social Security numbers over email.
Best Practices for Handling Email Attachments
Don’t open attachments unless you’re expecting them and you know who sent them. If an email attachment is suspicious, contact our Support Desk or your IT team before opening it.
As a general rule, if you don’t know the person who sent the attachment, don’t open it. Instead, delete the email immediately and let our Support Desk or your IT team know so we can be on the lookout.
Best Practices for Reviewing Email Links
Before clicking on any links, hover your mouse over them to see if the URL looks legitimate and is a trusted site.
If you still aren’t sure, open a new browser window instead of clicking on links and manually type in the address.
And lastly, as tempting as it may be, don’t click the “Unsubscribe” link in a spam email. Clicking it only lets the spammer know your address is legitimate, which could lead to you receiving more spam.
Never Reply or Send Personal information
I know it’s tempting, especially when you know it’s a scam but don’t reply. This is a forged email and will only send you further down the rabbit hole.
I’m sure it goes without saying, but – never give out your passwords, account numbers, credit/debit card information, social security number, medical information, or any other personal information via email.
Be cautious about where you enter your email address online. The internet is an incredible thing, but you shouldn’t blindly trust random websites. Spammers often scan unsecured websites to collect email addresses.
Steps to Prevent Fraudulent Payments
It seems like almost everything can be done with a simple push of a button these days. The convenience is nice, but it has also made us too trustworthy and a little lax at times when it comes to protecting ourselves.
A lot of billing-related communication is done via email, so scammers use this to their advantage. Their goal is usually to get you to send them money, and as already mentioned, they’ve gotten pretty good at impersonating people and organizations you trust.
Scammers will impersonate a client or vendor, and then they will request payments on their behalf online or over email. I know it sounds like a classic “it won’t happen to me” situation, but smart people are being tricked into paying millions of dollars because of scams like these.
The good news is, there are ways to defend yourself from these kinds of attacks.
Basic Guidelines for Preventing Fraudulent Payments:
As mentioned before, don’t send personal information in an email message. Reputable businesses will never ask for sensitive information via email.
Creating an approval process for payments that requires approval from at least two people will help prevent sending money or sensitive information to scammers. For example, have a manager and an accountant review the payment before processing.
You should also put a payment approval submission process in place. For example, if payment is by check, it’s good to have a rule stating that it requires two or more signatures if it is over a certain dollar amount.
This process will ensure that all your bases are covered.
Lastly, attacks will appear to come from management, long-time customers, partners, or vendors. Don’t ever break protocol, even if you know the person or company well. For example, if something is weird about a payment request from a vendor you’re familiar with, call that vendor directly. Use the phone number you’ve used in the past with them, not the number that may be located on the invoice or payment request in question.
This includes not accepting account changes via email — things like changes in their address, account number, or payment information. Those should be done over the phone via a trusted phone number.
Protect Your Southern California Business With Workplace Email Safety Best Practices
Keep in mind that email can be intercepted between leaving your inbox and its destination. So, applying the above rules to the emails you send and receive is very important.
And last but not least, be sure to log out or lock your workstation when you step away from it.
So, there you have it. While tedious at times, email safety will go a long way towards protecting you and your company’s information from scams, viruses, and hackers.