Everyone should worry about online safety. This is especially true when it comes to business and personal information, like banking records, payroll, or trade secrets.
And while passwords can go a long way, unfortunately, they are getting easier to crack.
So, what can you do? How do you protect your business from hackers and cybercriminals running amuck on the internet?
There is something that can make it a lot harder for cybercriminals, and it goes by the name of multi-factor authentication.
Multi-factor authentication isn’t new, but it is becoming much more available for small businesses. And believe it or not, this is a significant win.
Multi-factor authentication's one goal is to eliminate security breaches. By setting up multiple steps of verification, it has the power to stop hackers in their tracks.
So, let’s break this up into three categories: what is it, how does it work, and what does this solution look like.
What Is Multi-Factor Authentication?
Multi-factor authentication virtually eliminates security breaches due to lost, stolen, or weak passwords.
But how?
Do you remember the Bridge of Death from Monty Python and the Holy Grail? Multi-factor authentication is kind of like the bridge-keeper. You must know your name, your quest, and your favorite color to log in.
Okay, not exactly.
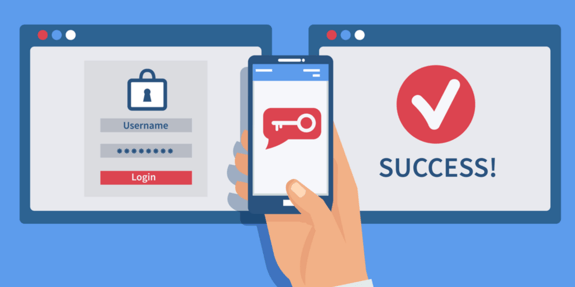
Multi-factor authentication has you enter your password, but it also has you verify your identity in at least one other way. It can be a text or call to your cell phone. Or even better, an alert or something similar on a mobile app.
In plain English: multi-factor authentication makes your company's data more secure by ensuring that users are who they say they are. What makes it unique is that it checks multiple times, in multiple ways to ensure that you really are YOU.
Attackers won't have access to all the methods of authentication, so access is denied. Your users can get in, and hackers cannot -- simple as that.
Think of it as a speakeasy. You only get access if you know ALL the passcodes.
How Does Multi-Factor Authentication Work?
Now, let's talk about how it works.
Multi-factor authentication solutions are third-party applications. They integrate with and supplement on-premise or hosted authentication -- what most people call a "login."
These tools require users to prove at least twice, using multiple methods, that they are a real user and not a hacker.
Common Authentication Methods
1. Something You Know
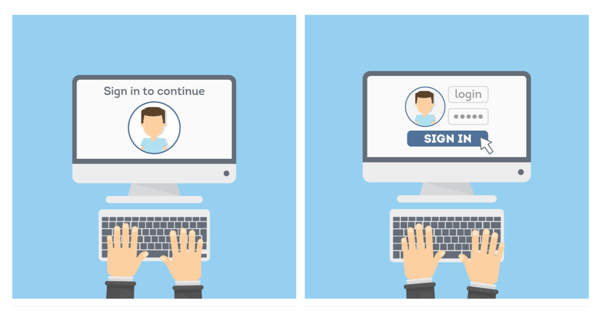
One of the most common authentications is a password, PIN, or code. Usually, this is the first step when you try to log in to your computer or open an application. It will ask you for a username and password, you type them, and press enter.
Rather than passwords, I really like pass-phrases. Using whole sentences, with punctuation and at least one number thrown in for added complexity makes pass-phrases hard to crack. Plus they're long and easy to remember.
You can try something like: My favorite 5hirt is a Cloud based pet.
Sure, it doesn't make sense, but you will remember it, and no one could possibly guess it.
2. Something You Physically Have
The next common type of authentication uses something that you have for authentication-- Ex: your phone, a security token for a one-time password, a smart card, or anything else along those lines.
You might be sent a text message with a passcode that needs to be entered or use your phone to scan a QR code on the screen.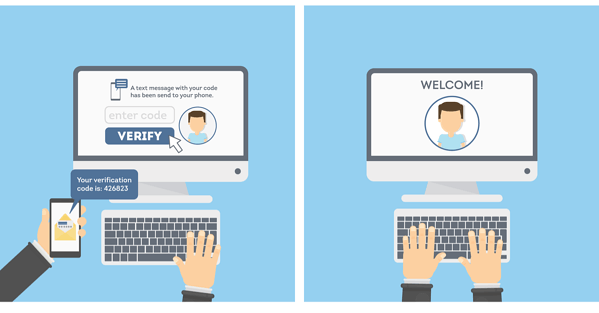
There are a number of possibilities, but it'll be something you receive or actively do that requires you to have physical access to a trusted device.
3. Something You Are
The next most common method uses something that you are for authentication -- your face, fingerprint, retina scans, or any form of biometrics.
If you have ever seen a James Bond or Mission Impossible movie, you know what I'm talking about. Top secret labs in movies and TV shows are always shown using biometrics to gain access to sensitive information.
But this isn't just something in the movies. Many of today's laptops and cell phones have the ability to use biometrics for authentication now too.
 (photo credit: Rachmaninoff - https:// Commons.wikimedia.org)
(photo credit: Rachmaninoff - https:// Commons.wikimedia.org)
Remember, you'll need two or more forms of authentication for it to actually be multi-factor authentication. Otherwise, you'll have the same vulnerabilities as traditional authentication.
Multi-Factor Authentication Modernized with Cloud-Based Solutions
Now that you know what it is and how it works, let's talk about some typical multi-factor authentication solutions.
It used to be pretty expensive to deploy multi-factor authentication solutions. Pricey security tokens and special software made it cost-prohibitive for small businesses.
Recently, Cloud-based technology has really changed the game for small businesses. With a Cloud-based application, there is nothing on-premise for you to manage or install. Being able to use them without needing a dedicated server or hardware has really helped to drop the price point.
Also, the advancement of smartphones (and the fact that pretty much everyone on the planet has at least one), means that the need to purchase costly specialized hardware has all but disappeared.
And like most Cloud services, it's generally priced per-user rather than per-deployment which again, brings costs down.
What to Look for in a Multi-Factor Authentication Solution
So, what are you looking for in a multi-factor authentication solution? -- Great question!
SMS or text messaging is a prevalent authentication method that should be avoided. Text messages can be easily intercepted and, therefore, are not very secure. Also, be careful with using phone calls as an authentication method. They have similar risks to text messages and can also be intercepted.
Your best bet today is to use QR codes for authentication. It's great because the user must physically be at the device that they're trying to access company resources from.
How QR Codes Work for Multi-Factor Authentication:
When a user attempts to log in, a little QR code will come up on their computer. The user then scans the code with their mobile device, which has previously been established as a trusted device.
You now know, for sure, that they're physically present at the access device because they scanned the code. And they are who they say they are because they used their trusted mobile device to scan it.
 (photo credit: PixaBay.com)
(photo credit: PixaBay.com)
Another similar option works by just sending a notification to a mobile app that the user then must approve or deny. This is also a useful method, but because the user does not have to prove that they are physically present, it’s not quite as strong as the QR code method.
Keep in mind that not all multi-factor authentication solutions are created equal. Work with your managed IT services provider or IT department to select the best one for your company's needs.
Remember, the most common way the bad guys can get access to your stuff is by either tricking your users into giving up their credentials or by guessing them using a brute-force method.
A solid password policy that requires long and complex passwords, that expire often, is essential, but still has vulnerabilities. Now that multi-factor authentication is widely available; you have the tools to help keep the bad guys away from your information, even if they know someone’s password!
Have questions? We're happy to chat anytime. Give us a call at 800-481-4369.
Related: 5 Password Policy Guidelines for Small to Mid-Size Businesses