On September 7th, a nearly full room of 30 business executives and managers came out to the Rancho Cucamonga Chamber of Commerce's Monthly Business Connection Network (BCN) Lunch.
VC3, Inc.’s Chief Operating Officer, Derek Woolf, was thrilled to present this month's speaker, Julio Martin from WatchGuard Technologies. Julio has been in the IT world for over 20 years and specializes in the security of small to mid-sized companies. Julio gave this one-time presentation on the state of cyber security in regard to ransomware and small businesses. WatchGuard leads the market with research and technology, which is why we’ve been deploying WatchGuard technologies to our customers for 15 years.
Here's a quick recap of Julios's event presentation with takeaways for business owners.

What is Ransomware and What Does It Look Like?
Starting from the beginning, what is ransomware? What does it look like and how do I know if it's affecting my company?
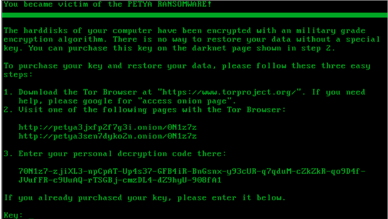
"There are quite a few different kinds of ransomware out there. Most people are familiar with crypto ransomware. It goes in and encrypts your system, then demands a ransom to get it back. But unfortunately, there are so many more types out there. Things like scareware that leverages fear to get you to pay for fake software. Or locking ransomware. It locks you out of your system until you've paid the ransom...the most popular right now is called PETYA Ransomware that has to be paid by Bitcoin."
Julio went on to say that ransomware is not a secret. It's everywhere all over the news. Hitting the health care sectors and even police branches. And what's worse, there have been several circumstances where these organizations have had to pay the ransom. This happens when there isn't a backup, it was the only way they could get their information back.
Here's what the PETYA Ransomware looks like if you're infected:
Where Does Ransomware Come From?
It's the big question.
"40% of spam attachments include ransomware, according to IBM X-Force, so we know how we are getting infected -- but where they come from is an entirely different question.
And still, 73% of top attacks target web browsers in drive-by download attacks. A drive-by-download is when a legitimate website is compromised. There is malware floating on it, and it'll attach itself, downloading ransomware, and the user doesn't see it -- meaning you don't have to go to the shady part of the internet to get infected anymore.”
Who’s Making and Spreading Ransomware?
That’s the kicker: there's no way of telling. It could be your neighbor or some guy in a basement in Russia. However, with tools like WatchGuard, reporting and analytics can be set to easily track these threats as they attempt to invade your network.
The Evolution of Ransomware
Ransomware is growing into a billion-dollar industry as predicted by the FBI. That's right BILLION with a "B." According to the 2017 Verizon Data Breach Report, ransomware cost U.S. victims $209M in Q1 of 2016. That alone is up 771% from Q1 2015.
Ransomware-as-a-Service
Ransomware is so popular with internet thieves, it’s now offered as a service. Ransomware-as-a-Service has emerged all over the web.
"You can get all your web services 'as-a-service' today, and now you can get ransomware as a service as well. Essentially, you can pay someone to set up your ransomware and walk your targets through the payment process. Yes, ransomware now how customer support! If you have the unfortunate luck of being attacked, you can call a help line, and they will walk you through how to make a payment, and how to get Bitcoin to pay the ransom.”
Not only are they offering customer service, they are also offering a one-time get-out-jail-free pyramid scheme card. If you have been infected and don’t want to pay or can’t pay, you can pass the viruses to 3 other people, and the hacker will let you go. Also, usually, you have about 72 hours to make a payment in full. If not your ransom can double or even triple.
How to Protect Your Company From Ransomware
"83% of our partners believe that ransomware will be their customers' #1 threat in 2017. So, it's important that you know what it is and what it looks like. For example, FedEx doesn't send shipping information via an attachment. You're not going to get your boarding pass from Delta as an attachment. Even so, ransomware attacks have quadrupled in 2016 - we estimate about 4,000 attacks a day. The potential cost of a crypto-ransomware attack on a midsize enterprise is $99K. So, for a small company, that can put you out of business."
Related article: Executive Guide to Cyber Security: Essential Information for Managing Business Risk
WatchGuard’s Three-Pronged Security Approach
WatchGuard uses a three-pronged approach as their best defense method: Prevent, Detect, and Respond. This three-pronged approach is on the spectrum of education, security, and recovery.
“There are no silver bullets; no single defense will protect you completely from computer attacks. You should take steps to prevent the initial infection by using a multi-layer security approach.
Beyond having layered security, educate your employees on how to spot phishing attempts. These continue to be the most common attacks for ransomware. Phishing and browsing awareness training is a must, and so it’s a regular IT update to your users.
Backups are essential to home and business. If you don’t have a backup plan, then you plan to lose your data.
But the plan isn’t enough; you should also regularly create and test offline backups to recover from in case of a ransomware infection. It’s important that your backup be offline to protect against ransomware that locates and encrypts network files shares.
Lastly, hire a professional. Security is not a destination, but a journey. It’s not set it and forget it. It requires maintenance, reporting, review, and custom altering to ensure you are safe. Having a trained, certified partner that can provide their services is critical.”
Tech Minute
Down to the minute with the latest news in the world of IT.


