As if we didn’t have enough to deal with during a pandemic, cyber criminals have increased their attempts to take over accounts, invade networks, kidnap data, and generally wreak havoc throughout 2020 and 2021.
Their tactics have evolved as technology has progressed, but the bad guys are still using tried-and-true social engineering tricks to bypass security layers, in addition to sophisticated software.
According to BitDefender, the pandemic was the overarching theme for malware and other cyber threats in the first half of 2020, and the volume of attacks has increased. For example, in May and June, they reported that 60% of all emails were fraudulent. And with so many people working remotely, hackers were doing everything they could to find vulnerabilities in home networks.
Vigilant Cyber Security Defense Required
No one knows when the pandemic will end, but one thing is sure – with or without COVID-19, cyber predators will continue to target people and systems for monetary gain.
When it comes to cyber threats, there never will be a time when we can just say, “Whew, I’m glad that’s over!” so we need to keep a vigilant defense.
Four Ways to Boost Your Cyber Security Defenses:
1. Verify Account Access with Multi-Factor Authentication (MFA)
Passwords, although a safety precaution, can be easy to crack. Many users disregard the need for their passwords to be strong, repeatedly using things like their mother’s maiden name, their birthday, or their dog’s name.
Multi-Factor Authentication (MFA) adds a layer of security so that even if a password is compromised, an intruder can still be stopped. There are different ways that MFA can be implemented, and there are authentication apps for both business and consumer use.
Authenticators work because they ask for something that an imposter could not possibly have – something you know, something you have (like your phone), something you are (like your fingerprint), or your location.
2. Train Your People to Spot Social Engineering Attempts
As we get better at protecting accounts with technologies like MFA, the bad guys are trying harder to bypass passwords entirely by using social engineering. Social Engineering uses deception and manipulation to trick people into doing something that will give them access to an account or a network.
The preferred method for social engineering is phishing which uses email as its delivery vehicle. The power of phishing is that the messages resemble legitimate communications that a person might receive from an entity either inside or outside their organization.
By all means, turn up the levels on your technical email security, but you must teach your people how to recognize things like look-alike domains, websites that ask to verify account information, and logos and messages that just seem a bit off.
Ongoing interactive security awareness training programs like KnowBe4 can be a valuable resource to keep training regularly.
As a manager, you’ll see both high-level and granular views of your most significant email phishing risk points, giving you the ability to manage it from there.
Here's what that can look like:
Combine ongoing cyber security training with business processes that require verification when a money transfer or release of private information is requested.
Related: Cyber Security & Risk Management Techniques for Business Managers
3. Implement Advanced Security Protections - Now!
The technology that cyber criminals use is becoming increasingly sophisticated with the evolution of Artificial Intelligence (AI) to locate an increasing number of targets and evade normal security layers. That means that unless you’re using AI to fight AI, you’re being outgunned.
AI is integrated into modern cyber security tools, making them faster and better at doing what they do than the generation before them. For example, upgrading your firewall to the latest version can give you Endpoint Detection and Response (EDR) capability. EDR enables you to detect and stop network intruders before they can do harm.
It’s possible you have some advanced security capabilities at your fingertips that might not be implemented yet.
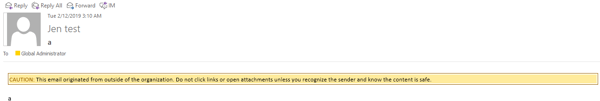
Microsoft 365 continues to increase the security features in its products, like adding the ability to flag external emails. This helps people identify potential phishing emails -- it may look like it’s from your CEO, but the “External email” warning tells people that it didn’t actually come from inside your company.
Here's an example of what that can look like:
4. Don’t Get Smished (SMS Phishing)
Just about everyone’s got a smartphone these days, and we’re using text messaging more and more instead of email or actual talking.
Cyber criminals know that we spend a lot of time in our messaging apps, so they’re trying to use that channel to get us to do something that will compromise security, like click on a link or give them private information. This is essentially phishing in SMS, and the term “SMShing” or “smishing” has emerged to describe this tactic.
Here's what SMShing can look like:
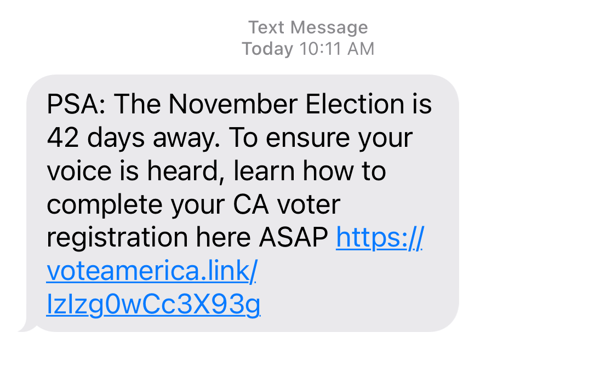 The same guidelines for dealing with email phishing also apply to SMS phishing.
The same guidelines for dealing with email phishing also apply to SMS phishing.
- Don’t reply to messages from people you don’t know.
- Don’t click on links or type in account information.
- Don’t let urgency get you to respond.
- Don’t take the bait.
Don’t Let Your Guard Down
Hackers will continue to switch up their tactics, using situations like the COVID-19 pandemic to try and take our guard down. Companies, regardless of size, will continue to lose data, money, and time if they allow a false sense of security or lack of security knowledge to lull them into complacency.
It’s an epic battle, as security experts and hackers work tirelessly to outsmart each other. But that doesn’t mean you shouldn’t TRY to protect yourself. Take security seriously to avoid the downtime, data loss, and expense that surrounds IT security breaches. Have a plan and work with your IT professionals to get the most out of your security.


